Patch Tuesday & Exploit Wednesday

Following this introduction to Patch Tuesday & Exploit Wednesday, we will be publishing key updates that have been released. Therefore please note these blogs are for information purposes only. Thus you should not make a business-critical decision without prior consultation with our team of industry experts.
At this point, our CREST Accredited Penetration Testers are returning to the office with millions of people across the UK. Unquestionably many industry leaders have observed and documented the sharp rise in cyber-crime and data breaches. In essence, the risk of a potential cyber security or data breach has significantly increased over the past 18 months.
What is Patch Tuesday & Exploit Wednesday?
Firstly the vast majority of people use a Microsoft Windows or Apple product at work or whilst running their business. In reality, modern software is written on complex code. This means when errors are recognised businesses need to go back and apply a patch to fix the problem. In short, patches are fixes for errors or mistakes that have arisen and need to be corrected.
Why Patch Tuesday & Exploit Wednesday matters:
- Firstly all businesses use operating systems or applications. Ethical Hackers inform providers regularly of errors in the code that they have used for using their products. In summary, failing to update and patch operating systems and applications alike can result in data breaches.
Do you use any of the following?
- Operating System – Microsoft Windows, Apple IOS, Android OS, Linux
- Application – Zoom, Microsoft Word. Teams
- Network Equipment – Routers, IOT, Video Cameras, smart printers, remote devises
Whether it’s an operating system or network equipment the use of IOT, applications and software are integral to our business-as-usual activities. As a result, system administrators need to keep up to date with operating systems vendors, application vendors and network equipment vendors who provide the required patches and remediation actions to remove any threats or errors in the software or applications they are using across the business.
Why does my business need cyber security?
- Comparatively patching alone will not provide 100% security to your systems. Evidently, it goes a long way towards safeguarding, but should go hand in hand with regular testing of your network. Therefore successful companies understand how to boost customer confidence and engagement. Regularly protecting their data through pen testing and correcting any vulnerabilities in their IT networks, applications or systems.
Exploit Wednesday

Once IT providers recognise a vulnerability in their products, anyone and everyone can take advantage of this. This means that malicious hackers can use the errors in the operating system or applications you use to exploit and breach your network. This doesn’t have to come from an external source, in some cases an honest mistake can result in data breaches and significant harm to your business. Any company that isn’t on the ball with patching and cyber security runs a very real risk of a significant data breach or getting hacked.
What does getting hacked look like?
- Defacing company website
- Ransomware (encrypting data and only unencrypting it for vast sums of money)
- Ruining the reputation of your company and thus any clients or customers avoiding using you ever again.
What can we do as a business?
- Subscribe to our monthly newsletter
- Patch your systems, applications and devices.
- Implement regular penetration testing.
- Train all staff on cyber security principles and best practice when working remotely and in the office.
- Consider monthly non-disruptive and cost-effective vulnerability assessments
The comparatively small cost of upping your annual security budget to include penetration testing, vulnerability assessments and cyber security training for all staff and regular patching as a form of defence is far more appealing than the risk of suffering the vast costs if you were to get hit by a cyber-attack.
Penetration Testing with CDS:
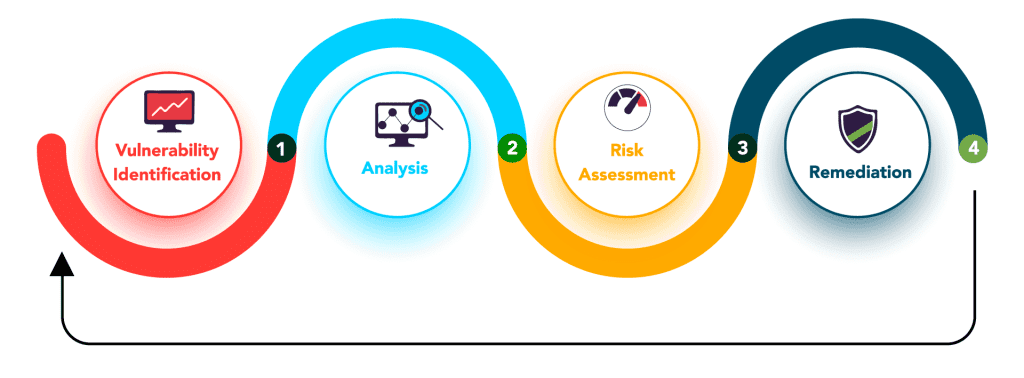
Our penetration testing service will provide you with a point in time analysis of your susceptibility to a cyber-attack. Our CREST accredited testers identify and assess the vulnerabilities that pose a threat to your network and systems. Once identified, our comprehensive report will determine the probability or risks associated with your systems or networks and what steps are required to mitigate against the possibility of a data breach.
Our penetration testing service provides you with:
- A ranked list of identified vulnerabilities in priority order (point in time analysis)
- The likelihood and probability of the exploitation of your current vulnerabilities
- A series of actions or mitigating steps to resolve or reduce the vulnerability
For more information on our pen testing service please get in touch via the website. We will be releasing newsletters outlining all the patches and key vulnerabilities in the monthly roundup. https://compliancedirectsolutions.com/pen-testing/
For more info on Patch Tuesday & Exploit Wednesday visit: https://en.wikipedia.org/wiki/Patch_Tuesday

